AVOIDING RANSOMWARE
Avast! - Pirates! They're not just on the high seas anymore. The pirates in this new age are Cyber-Buccaneers. And they will pillage and plunder and rifle and loot! Their new tactic, Ransomware! You've heard about it, and lately you've probably seen a lot about it on the news. Atlanta being held hostage. Companies such as Equifax, FedEx, and Boeing are paying a heavy price for not simply updating their computers with the latest in software patches. Under Armour just announced that their health app, MyFitnessPal was hacked - that's 150 Million accounts! That's more than the population of Japan! Liability, lawsuits, account information and sensitive financial files being hidden or encrypted, stolen, and destroyed. These attacks are sudden, pervasive, and will leave you wishing you had protected your network sooner.
Viruses and Ransomware have become a strange new reality. So what can you do to prevent these attacks from bogging down or hijacking your data and causing network collapse? First, it may help to understand what will happen if you don't. A seemingly random attack on your IT infrastructure will start without you knowing. Most attacks begin by opening the wrong email that launches a "worm" that into your system, or an electronic intrusion from an unknown subject/s on the outside. The virus or hacker will then search your data for mission critical files or material you have saved on active drives and backups, encrypt that data, and now it's useless or unidentifiable. You will receive a notice that you have been targeted and for a price they will unlock those files, usually after copying and distributing them to the highest bidder. Basically, your work becomes the winsome wench on the auction block - and they all wants the redhead!
Now, how to make sure this doesn't happen to you and your business. Knowing where the vulnerable access points are and taking proactive steps to eliminate potential threats is a great place to begin. That's where you need a qualified, professional IT management partner. Get Duplicated Managed Services - and friendly ships be on the horizon.
Dead networks tell no tales! Keeping cyber-buccaneers at bay should be a current priority for your IT solution or department. Break/Fix problem solvers will be too late. Add to that, 50% of Ransomware victims don't even get there data or network back, even after paying. How expensive would it be to your business to have your data stolen, your PC's locked, and your network inaccessible for hours on end? How about days? Many companies find themselves rebuilding their entire network from the ground up after a successful "cryptoviral" attack. How much would that cost you?
PROPER NETWORK SECURITY:
OK, enough with the Pirates references. I don't even know when "Talk Like a Pirate Day" is. What I do know is that without proper monitoring and detection methods your network, and all of your data, can potentially be accessed and/or stolen. Depending on what type of business you are or what industry you are in, your data even being searchable can be a serious legal matter. Now, what if your business doesn't have to adhere to HIPAA law or doesn't have National Security clearance or secrets? Well, the good part is that you will have the same protections and safeguards as if you did - and don't think that just because you're a small firm that your business just wouldn't be targeted, because it happens every day to every sized company there is. Its technical term is cryptoviral extortion and according to the Federal Bureau of Investigation (FBI) successful attacks since 2013 have accrued tens of millions of dollars for the hackers.
Just having stronger password protection in place and changing each password on a regular basis can be a great first step. The following are examples of the types of possible attacks that have been reported -
The most common attacks include:
1: Scareware
2: Encrypting Ransomware
3: Non-Encrypting Ransomware
4: Leakware (or Doxware)
5: and Mobile Ransomware
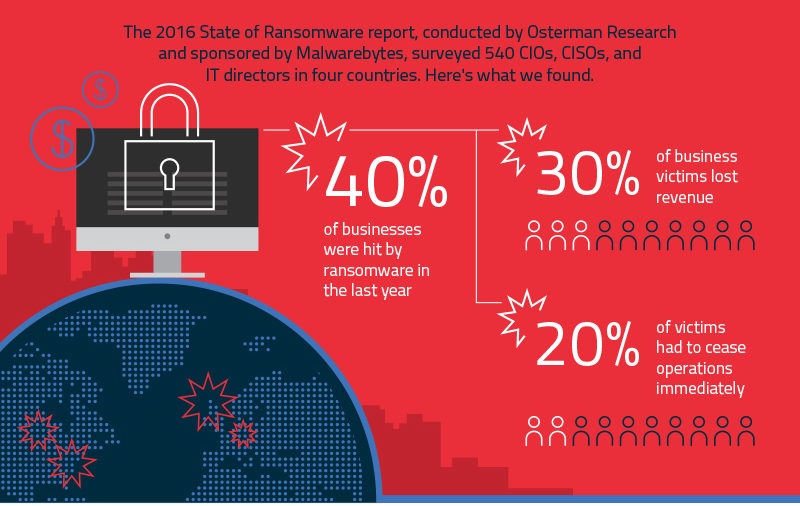 2016 Statistics show a staggering 752% increase in the number of Ransomware "families," or named hackers and groups, with another roughly 33% increase for 2017.
2016 Statistics show a staggering 752% increase in the number of Ransomware "families," or named hackers and groups, with another roughly 33% increase for 2017.Scareware is typically released by a Trojan Horse style virus, or "worm." Someone at your business can upload it without even knowing either from Email or by connecting an infected personal device. It has a hidden launch countdown and then suddenly the virus invades "Troy" - in this case your network. What happens in this scenario is an official looking scare tactic that puts a graphic up on your screen telling you that your system has been used for unlawful activity such as "pirated" media, or worse. The graphic may have official law enforcement agency logos and may declare that you now must pay a "fine" to unlock your system. Other data kidnapping attacks involve  the malware being introduced to your system through various means, encrypting your data, notifying you and demanding payment, and when paid, the key to reversing the encryption is then delivered. Digital currency like Bitcoin has made these types of electronic extortion schemes easy and very lucrative. In the Leakware tactic the cyber-attacker gains access to embarassing or proprietary data and threatens to publish it in order to damage your reputation or organization. Even just proof of a successful attack can be damaging in some instances. These attacks have been extremely productive in both the Financial and Healthcare industries and remain a constant threat there, but don't underestimate the ability for a hacker to come after your small business or even home computer. They can even target your phone. Mobile ransomware attacks mainly smartphones and loads a screen blocking message or page on top of your existing applications and can even attempt a form of clickjacking by causing you to accidentally give it "device administrator" access so that it can bore deeper into your phone's operating system. Typically this type of malware only affects Android users, but iPhones are not exempt from electronic snooping and "phishing" - passively accessing and using your stored data and even logged phone habits. These attacks can range from the absurd and easy to get rid of to very sophisticated random and impossible to break encryption key generators. And malicious software is just getting more and more advanced. Having a trusted advisor and partner for your IT infrastructure who understands the vulnerable insertion points and installs and properly configures the right antivirus measures is your key to avoid these disasters.
the malware being introduced to your system through various means, encrypting your data, notifying you and demanding payment, and when paid, the key to reversing the encryption is then delivered. Digital currency like Bitcoin has made these types of electronic extortion schemes easy and very lucrative. In the Leakware tactic the cyber-attacker gains access to embarassing or proprietary data and threatens to publish it in order to damage your reputation or organization. Even just proof of a successful attack can be damaging in some instances. These attacks have been extremely productive in both the Financial and Healthcare industries and remain a constant threat there, but don't underestimate the ability for a hacker to come after your small business or even home computer. They can even target your phone. Mobile ransomware attacks mainly smartphones and loads a screen blocking message or page on top of your existing applications and can even attempt a form of clickjacking by causing you to accidentally give it "device administrator" access so that it can bore deeper into your phone's operating system. Typically this type of malware only affects Android users, but iPhones are not exempt from electronic snooping and "phishing" - passively accessing and using your stored data and even logged phone habits. These attacks can range from the absurd and easy to get rid of to very sophisticated random and impossible to break encryption key generators. And malicious software is just getting more and more advanced. Having a trusted advisor and partner for your IT infrastructure who understands the vulnerable insertion points and installs and properly configures the right antivirus measures is your key to avoid these disasters.
DUPLICATED NETWORK SECURITY & SAFEGUARDS:
With these attacks on the rise coupled with the fact that they are extremely effective means that you can no longer just hope to avoid such a seemingly random event. Having the proper safeguards in place along with software that is kept up to date will minimize the overall threat. In fact, with network monitoring and regular updates to your system, electronic ransom or extortion can be virtually eliminated by never being able to insert or launch in the first place. Contact us here at Duplicated Business Solutions and we can make sure that your network has the latest in protections that companies like Boeing and FedEx should have utilized - but didn't.
Don't give up the ship!
A secure IT solution is just a click away. Now that you understand the main points about ransomware and cryptoviral attacks and their potential effects on your business, it’s time to make sure that you are taking the proper measures to calmer seas.
Smooth Sailing!
Stephen
For more information on Secure Printing environments and creating a protected IT Network, just follow the link:
Submit your comments by filling out the comment form below.
To access the source materials for this blog, check out Forbes online, and the article, https://www.forbes.com/sites/leemathews/2018/03/30/boeing-is-the-latest-wannacry-ransomware-victim/#758ec6e56634 by Lee Mathews, March 30, 2018 as well as his article from March 23, https://www.forbes.com/sites/leemathews/2018/03/23/city-of-atlanta-computers-hit-by-ransomware-attack/#1a7408042ee4. Fortune, and Bloomberg's: http://fortune.com/2018/03/29/myfitnesspal-password-under-armour-data-breach/ from March, 30, 2018. And the Technology section of The Washington Post, https://www.washingtonpost.com/business/technology/data-breach-hits-saks-fifth-avenue-lord-and-taylor-stores/2018/04/01/e3cc8aa6-35cc-11e8-af3c-2123715f78df_story.html?utm_term=.dfae6981ecc1 by Matt O'brien, April 1.